Why this happens
By default, users who join a Windows device to Microsoft Entra ID (Azure AD) can be granted local administrator rights on that device.
In many environments, this is not desired because it increases endpoint risk and reduces control.
How to stop it
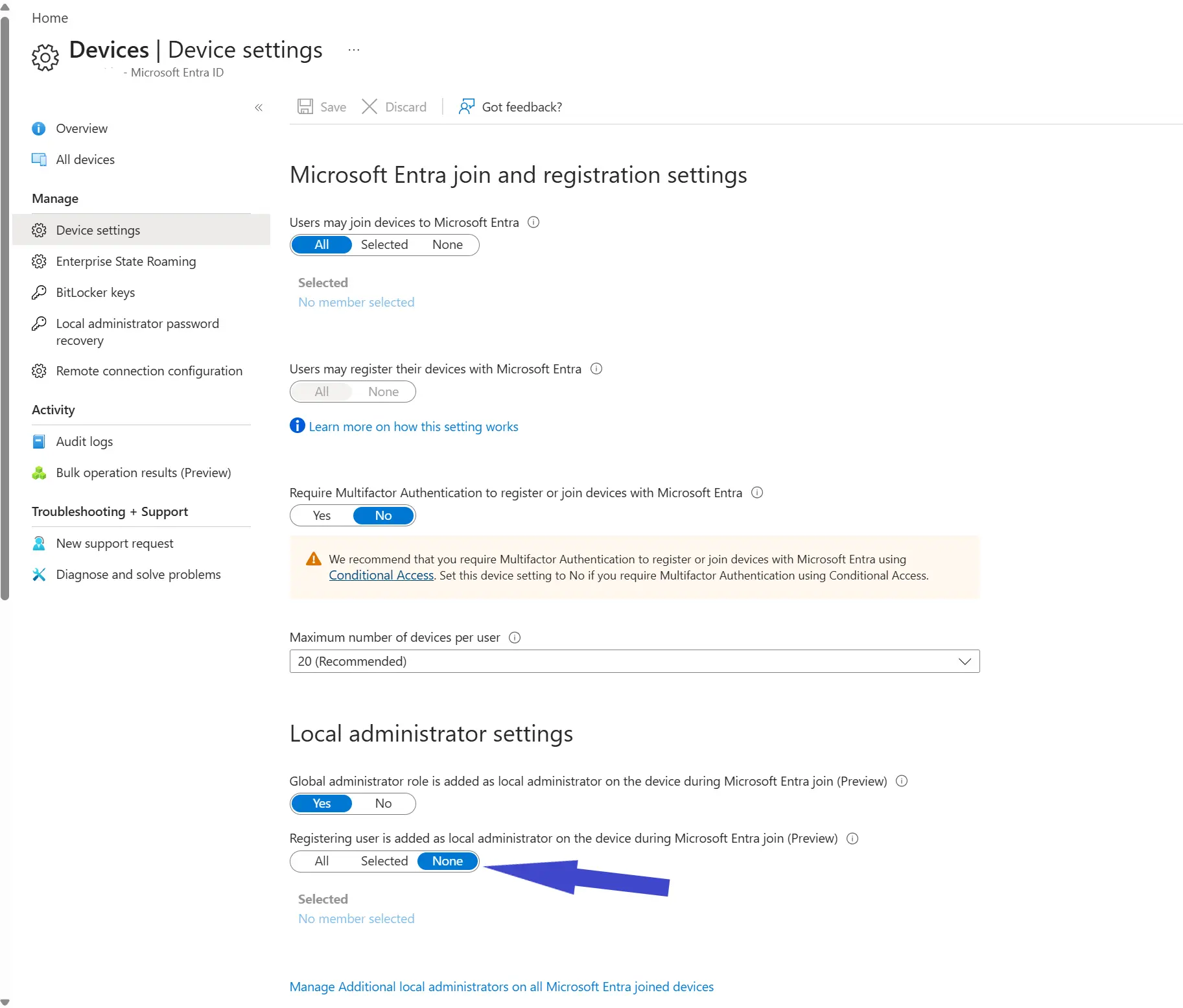
In the Microsoft Entra admin center, go to:
- Devices
- Device settings
Then set:
- Registering user is added as local administrator on the device during Microsoft Entra join -> None
You can also choose Selected if you want only specific users to receive local admin rights during join.
Visual reference
Recommendation
Set this to None as your default baseline, and use endpoint privilege management or controlled local admin assignment for exceptions instead of broad default admin rights.